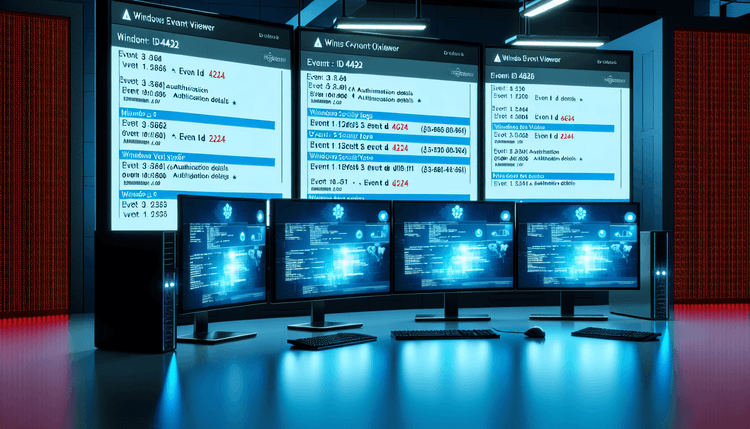
Event ID 4723 represents a critical security audit event that Windows generates when password change operations occur across the network. This event is part of the Account Management audit category and requires proper audit policy configuration to capture these activities effectively.
The event structure includes several key fields: the subject (who initiated the change), the target account (whose password was changed), and contextual information such as the source workstation and process details. Windows generates this event on domain controllers when processing password changes for domain accounts, and on local systems when changing local user passwords.
Understanding Event ID 4723 is crucial for security administrators managing Windows environments in 2026. With the increased focus on zero-trust security models and enhanced audit requirements, this event helps organizations maintain visibility into password management activities. The event works in conjunction with Group Policy settings and Advanced Audit Policy Configuration to provide comprehensive password change tracking.
Modern Windows deployments often integrate Event ID 4723 monitoring with SIEM solutions and security orchestration platforms. The structured event data enables automated analysis and alerting when suspicious password change patterns emerge, supporting proactive security monitoring and incident response capabilities.