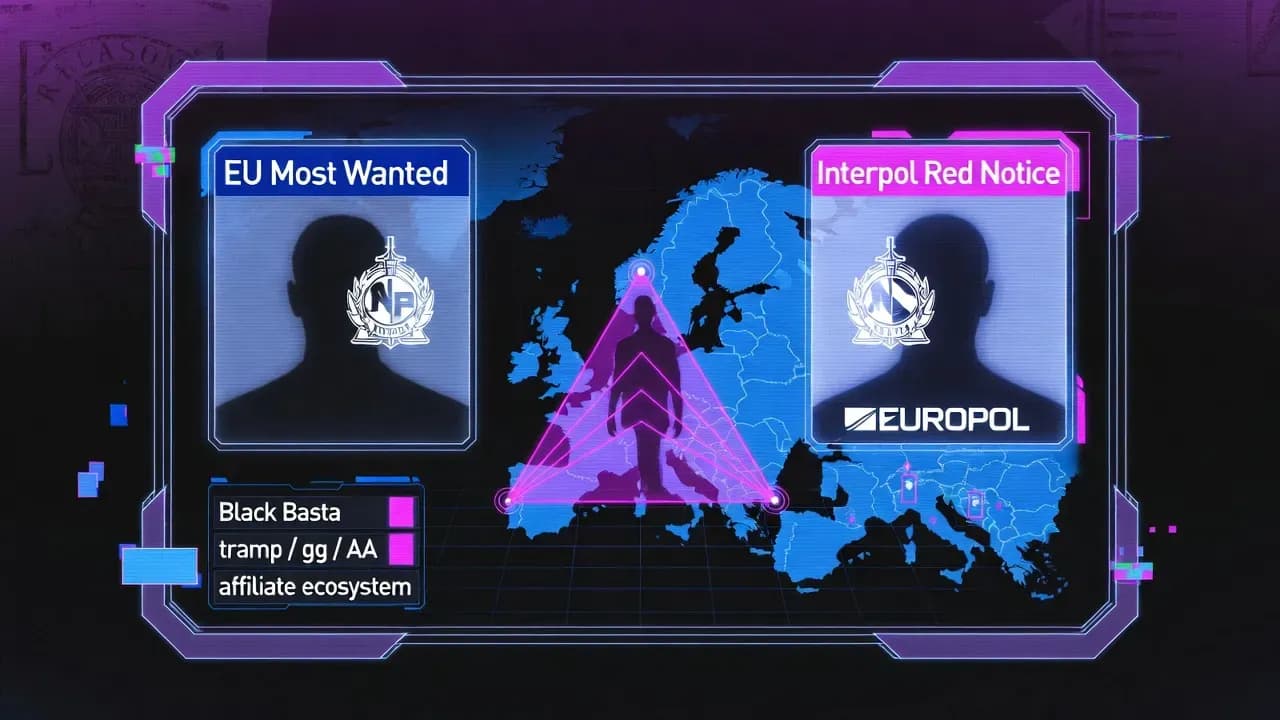
Black Basta boss added to Interpol Red Notice: what the hunt for Oleg Nefedov changes for ransomware defense
Black Basta's alleged leader Oleg Nefedov is now on Interpol's Red Notice. What this means for defenders, victims, and the ransomware ecosystem in 2026.
The addition of Black Basta's alleged leader to an Interpol Red Notice is more than a symbolic escalation. When a ransomware operation's command layer is publicly named, photographed, and tied to formal arrest requests, it changes the economics of the ecosystem around it: affiliates become risk-averse, infrastructure providers reassess exposure, and cash-out routes get harder to sustain at scale. Ukrainian and German authorities say they have identified Oleg Evgenievich Nefedov, a 35-year-old Russian national, as a key figure behind Black Basta, and reporting indicates he has now been listed publicly across European and international wanted channels.
For defenders, this is not "feel-good news" to consume and forget. Black Basta was widely linked to double-extortion campaigns affecting large organizations, and the group's operational model fits a pattern that rarely disappears cleanly. Even when one brand goes quiet, the playbook and people often reappear under new names, new malware families, or new affiliate programs. The practical question is whether this law enforcement visibility creates enough friction to reduce threat volume, or whether it simply triggers a reshuffle.
What happened: the technical and operational breakdown of the identification
According to reporting on the investigation, German authorities have identified Nefedov as the leader of Black Basta and Ukrainian police, working with German counterparts, carried out searches tied to additional suspects in western Ukraine. Investigators described these suspects as specialists involved in breaking into protected systems and "hash cracking" to obtain passwords, which points to a familiar ransomware supply chain: credential theft, privilege escalation, lateral movement, then encryption and extortion.
That matters because it aligns with how modern ransomware groups scale. Many high-volume crews do not run every stage themselves. They rely on specialists who either sell access (initial access brokers) or provide services like password cracking, data exfiltration staging, and infrastructure. When law enforcement describes roles in this way, it is effectively confirming the operational segmentation defenders already see in incident response.
The "Interpol Red Notice" angle also needs precision. A Red Notice is not a global arrest warrant issued by Interpol itself. Interpol describes it as a request to law enforcement worldwide to locate and provisionally arrest a person, pending extradition or similar legal action, with each country applying its own laws and thresholds. In practice, that means the notice's impact depends heavily on geography and politics. If a suspect remains in a jurisdiction unlikely to cooperate, the effect is indirect: constrained travel, reduced ability to move money, and more pressure on collaborators.
Who is exposed: victims, sectors, and why Black Basta's model was hard to contain
Black Basta emerged as a ransomware-as-a-service style operation in 2022 and was repeatedly associated with large victim profiles. Public reporting has listed victims across manufacturing, healthcare, technology services, and the public sector, which is typical of double-extortion crews optimizing for payout probability rather than ideological targets.
One reason Black Basta became a persistent problem for enterprises is that their campaigns map to common "enterprise reality" weaknesses. Credential reuse, exposed remote services, weak segmentation, and over-privileged accounts allow a ransomware affiliate to move from one foothold to domain-level control quickly. Once attackers have admin credentials, they can disable security controls, locate backup systems, and exfiltrate data for leverage.
German law enforcement summaries cited by other outlets describe the group as responsible for extortion against more than 100 entities in Germany and approximately 600 more worldwide. While every number should be treated carefully, the scale is consistent with the broader industry understanding: Black Basta wasn't a niche crew, and its operational tempo made it a constant threat for incident response teams.
Threat actor profile: why Nefedov's alleged ties to earlier ecosystems matter
A key analytical point is continuity. Reporting around Black Basta has long focused on possible overlap with the Conti ecosystem and its aftermath. This is strategically important because Conti's fragmentation did not reduce ransomware capacity, it redistributed it. When large syndicates splinter, experienced operators migrate into smaller, more agile groups, often carrying tooling, negotiation tactics, and affiliate relationships with them.
The Black Basta chat leak from 2025 intensified this discussion because it offered a rare view into internal conversations, hierarchy, and operational practices. One widely-cited metric from that leak is the scale: more than 200,000 leaked messages were referenced in analysis and coverage, which helped researchers map identities and roles with more confidence than typical OSINT alone.
What should defenders take from that? Leaks and arrests can weaken brand cohesion, but they also teach the broader underground what failed. The next generation often becomes more disciplined: better compartmentalization, fewer persistent handles, and more careful infrastructure separation. So while naming an alleged leader can be disruptive, it can also prompt the ecosystem to adapt in ways that are harder to investigate later.
How organizations can respond: practical actions that still matter even if the group "declines"
Law enforcement wins do not patch your environment. If you want to translate this news into reduced risk, treat it as a prompt to pressure-test your ransomware resilience and confirm that the controls you rely on would work during a real intrusion.
Start with identity controls, because most ransomware incidents are identity incidents in disguise. Enforce phishing-resistant MFA where possible, reduce standing privileges, and remove local admin sprawl. If your environment still relies on shared admin credentials, you are structurally vulnerable to the exact "password extraction and privilege escalation" role described in the investigation.
Next, validate that you can actually contain lateral movement. Segmentation is often documented but not enforced. Run tabletop exercises that assume the attacker has a valid VPN session and an internal admin token, then ask whether you can stop them from reaching backup systems, hypervisors, and identity infrastructure. If the answer is "not quickly," prioritize segmentation and monitoring around those assets.
Finally, treat backup integrity as a security engineering problem, not a storage problem. Immutable backups, offline copies, and tested restoration procedures are what separate a painful incident from an existential one. Many ransomware crews are optimized to delete or encrypt accessible backups early in the kill chain.
Lessons learned: why Interpol Red Notice events still matter to defenders
It is easy to dismiss wanted listings as political theater. That would be a mistake. These events often correlate with meaningful downstream changes: sanctions pressure, exchange compliance tightening, and more aggressive tracking of infrastructure and money flows. Even if the suspect is not arrested immediately, the network around them is forced to operate under higher friction.
Equally important is what this signals about international cooperation. In this case, reporting points to Ukrainian and German collaboration, and public summaries reference broader European involvement. For defenders, that suggests a gradual improvement in cross-border operational tempo, which is historically one of the main constraints in cybercrime enforcement.
The more strategic implication is deterrence-by-cost. Ransomware persists because it is profitable and relatively safe for operators in certain jurisdictions. Public identification, travel constraints, and increased operational security costs do not end the business, but they can reduce scale and increase mistakes, which defenders can exploit.
Prevention and detection strategies: the controls that hit ransomware where it hurts
If you want to make ransomware less viable in your environment, focus on four areas that reliably disrupt campaigns:
First, harden initial access paths. Exposed remote services, insecure VPN configurations, and weak email authentication remain top risk multipliers. Even basic improvements such as conditional access, geo-risk policies, and strict MFA enforcement can shut down entire classes of credential-based intrusion.
Second, watch for credential cracking and privilege escalation indicators. The investigation language around hash cracking is a reminder that attackers still invest heavily in turning captured hashes into reusable credentials. Set up detections for suspicious credential dumping, abnormal Kerberos activity, and unusual privileged logons, especially from systems that should not authenticate broadly.
Third, monitor the "quiet phase." Ransomware affiliates typically spend time enumerating the domain, locating file shares, and staging data exfiltration. If your telemetry only lights up at encryption time, you are already late. Invest in detections for large archive creation, unusual outbound data flows, and administrative tool abuse.
Fourth, prepare your comms and legal workflow. Double-extortion puts pressure on decision-making under time constraints. A rehearsed process for incident response, legal review, and executive decision gates is a defensive control in its own right, because it prevents panic-driven mistakes.
Closing perspective
The Black Basta boss Interpol Red Notice story is best understood as a pressure event against the ransomware ecosystem, not a finish line. Naming Oleg Nefedov and elevating the case through international wanted channels can raise operational costs and disrupt parts of the affiliate economy, but it does not remove the underlying conditions that ransomware exploits: weak identity hygiene, over-privileged environments, and inadequate recovery planning. If you want this news to reduce your risk in 2026, use it as the trigger to validate identity controls, segmentation, and restoration readiness, because the next "Black Basta" will not announce itself in advance.
Frequently Asked Questions
A Red Notice is a request to law enforcement worldwide to locate and provisionally arrest a person pending extradition or similar legal action. Interpol explicitly notes it is not an international arrest warrant, and each country decides what action to take under its own laws.
Not necessarily. Public identification can disrupt leadership, travel, and finances, but ransomware ecosystems often persist through rebranding and affiliate migration. Defenders should assume tactics and tooling can reappear under new names even if a brand goes quiet.
Because credential access is a major scaling mechanism for ransomware. If attackers can crack passwords from captured hashes and escalate privileges, they can disable defenses, reach backups, and deploy ransomware broadly across the domain. Investigation summaries describing these roles align with common incident response patterns.
Large enterprises, healthcare, public-sector organizations, and critical suppliers remain high-risk because they combine sensitive data with operational pressure to restore services quickly. Reporting around Black Basta has repeatedly referenced major organizations across these categories.
Yes, but mostly indirectly. If a suspect remains in a non-cooperative jurisdiction, the notice can still restrict travel, complicate money movement, and increase pressure on collaborators and service providers. That friction can reduce operational tempo even without an arrest.
Validate identity and recovery readiness. Strong MFA, reduced privileges, and tested restores are the controls most likely to break a ransomware campaign's economic model, regardless of which group is active this quarter.




Comments
Want to join the discussion?
Create an account to unlock exclusive member content, save your favorite articles, and join our community of IT professionals.
New here? Create a free account to get started.