
The 3-2-1-1-0 Backup Rule Explained (NAS, Cloud, Immutability, and Ransomware Reality)
A premium, practical guide to the 3-2-1-1-0 backup rule. Learn how ransomware targets backups, how i...
Tutorials, guides, and explanations for all skill levels

Most ransomware recoveries fail for predictable, repeating reasons—not because backups are fundamentally broken, but because the backup plane shares the same security perimeter as production. This gui...
Start learning
A premium, practical guide to the 3-2-1-1-0 backup rule. Learn how ransomware targets backups, how i...
A complete beginner explainer: how cyberattacks really happen, CIA triad, the 6-step attack chain, Z...

Error 0x8004de40 usually means the OneDrive sync client can't establish a secure connection to Micro...

KB5068787 (OS Build 20348.4405) is a Windows Server 2022 cumulative security update. This guide walk...
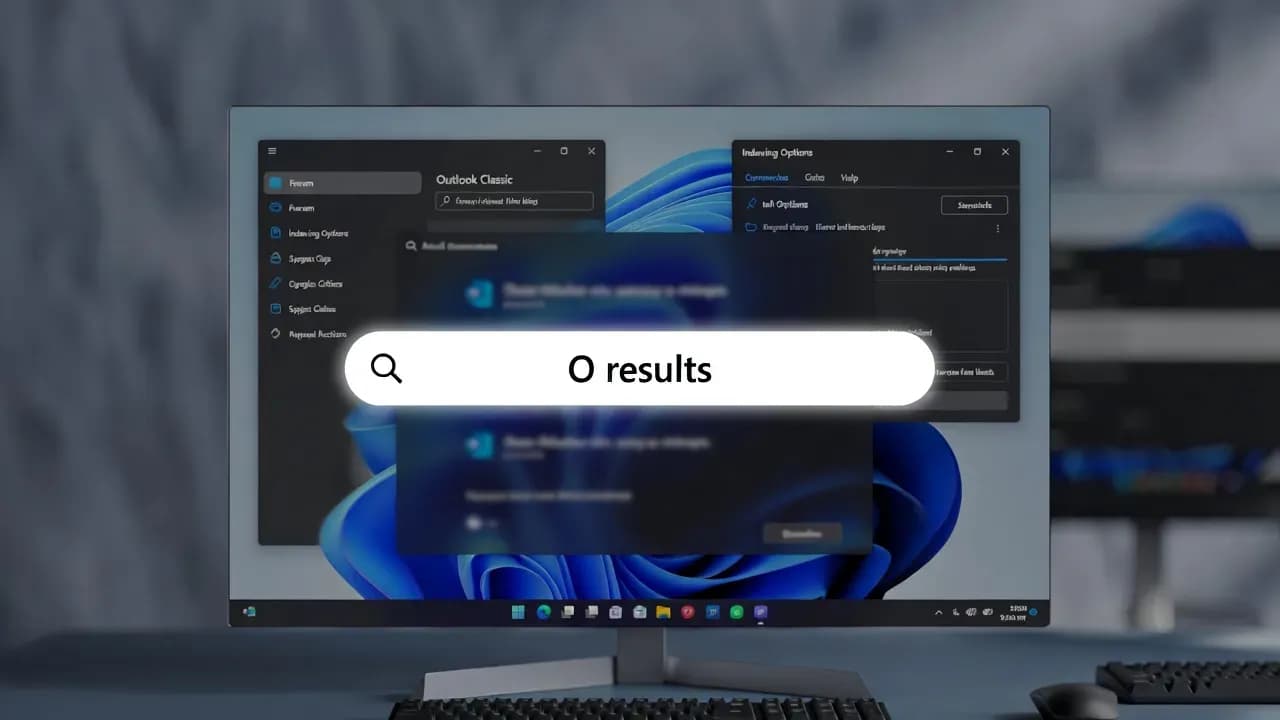
When Outlook Classic search returns no results, misses older emails, or only searches subject and se...
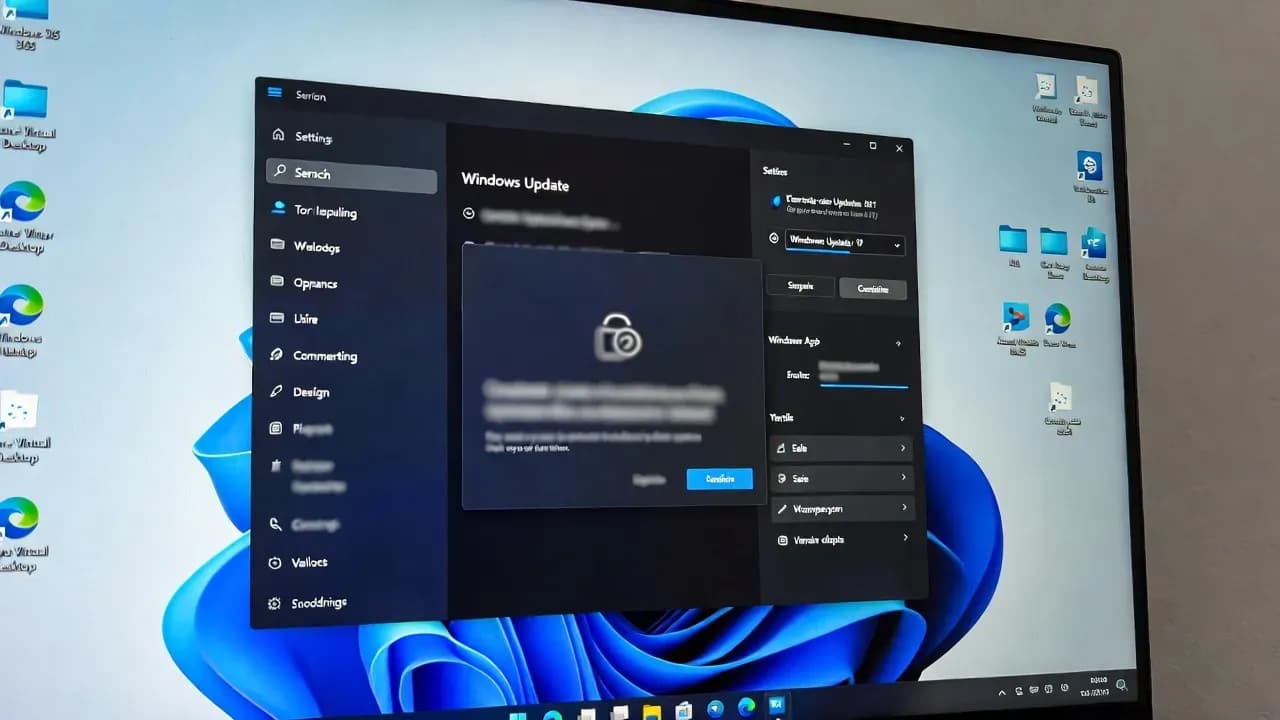
After installing KB5074109 (January 2026 Patch Tuesday), some Windows 11 25H2 and 24H2 devices can h...

Outlook Classic repeatedly asking for your Microsoft 365 password is almost never about the password...

If File Explorer briefly flashes bright white in Windows 11 dark mode, you're likely hitting a known...

When the Windows 11 search bar stops working, the cause is usually a stuck SearchHost process, a bro...

If Windows 11 became slow right after an update, the cause is usually one of three things: post-upda...

Endpoint Privilege Management replaces standing local admin rights with controlled, auditable elevat...

Active Directory and Azure AD share a name and both "do identity," yet they were built for different...

KB5068787 is the November 2025 cumulative security update for Windows Server 2022, bringing systems...

Step-by-step guide to reset a forgotten VMware ESXi root password using a Linux Live CD. Works on ES...

Learn how to completely remove Microsoft Copilot, Recall, and all AI features from Windows 11 using...

Ransomware has evolved from a billion-dollar criminal enterprise that can cripple organizations in m...

SD-WAN (Software-Defined Wide Area Network) is a modern networking technology that uses software to...

VPNs assume everyone inside is trustworthy. That assumption is why breaches spread. ZTNA flips the m...