Malware
Malware detection, analysis, and removal guides for IT security.
Articles with this Tag
 Security
SecuritySandworm's DynoWiper Malware Targets Polish Power Sector
Sandworm's DynoWiper malware targets Polish power sector in attempted cyber attack
 Security
SecurityNorth Korea–Linked "Contagious Interview" Hackers Abuse VS Code Projects to Execute Backdoors When Developers Trust Repos
DPRK-linked actors behind the long-running Contagious Interview campaign are pushing malicious Git r...
 Security
SecurityCrashFix Chrome Extension Campaign Delivers ModeloRAT via "ClickFix" Browser-Crash Lures
A fake Chrome ad blocker crashes browsers to push ClickFix commands, then deploys ModeloRAT on domai...
Basics of Cybersecurity (2026): A Premium Beginner Explainer (That Actually Teaches You)
A complete beginner explainer: how cyberattacks really happen, CIA triad, the 6-step attack chain, Z...
 Security
SecurityRustyWater RAT: MuddyWater Deploys New Rust Backdoor Targeting Middle East
Iranian APT group MuddyWater deploys RustyWater, a new RAT written in Rust, via sophisticated spear-...
 Security
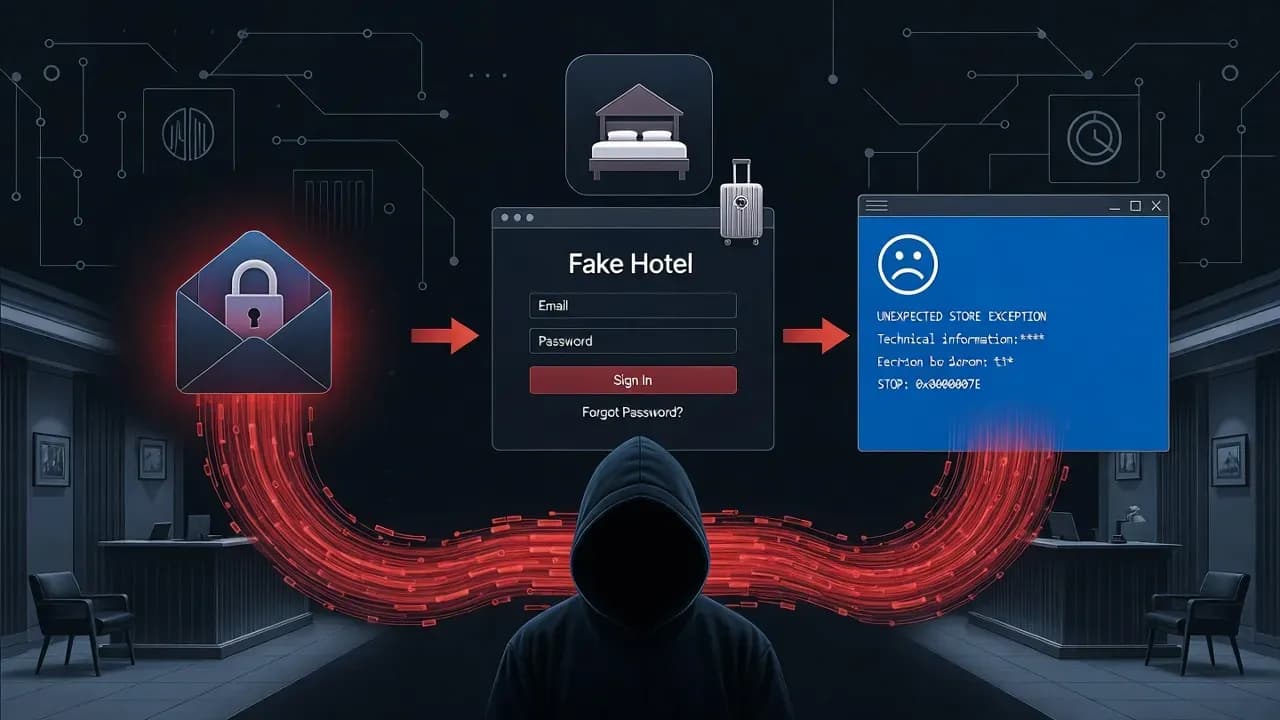
SecurityPHALT#BLYX: Fake Booking.com Emails and ClickFix BSoD Trap Deploy DCRat Malware on Hotel Systems
Threat actors are weaponizing fake Booking.com reservation cancellations and simulated Blue Screen o...
 Security
SecurityPhantom Shuttle: Fake VPN Chrome Extensions Steal Credentials from 170+ High-Value Domains
Two identically-named Chrome extensions masquerading as legitimate VPN services have been secretly i...
 Explainer
ExplainerWhat Is Ransomware and How to Protect Against It
Ransomware has evolved from a billion-dollar criminal enterprise that can cripple organizations in m...
 Security
SecurityGoBruteforcer Botnet Targets Crypto and Blockchain Projects in New Attack Wave
Security researchers have uncovered an evolved version of the GoBruteforcer botnet actively targetin...
 Security
SecurityownCloud Warns of Massive Credential Theft: Enable MFA Immediately
ownCloud has issued an urgent security advisory following a Hudson Rock report revealing that dozens...
 Security
SecurityKimwolf Botnet Weaponizes Residential Proxies to Infiltrate Your Home Network
A massive new botnet is rewriting the rules of network security. Kimwolf exploits a vulnerability in...
 Security
SecurityClickFix Malware Uses Fake Windows Update Screens to Infect PCs
New variants of ClickFix social engineering attacks are evolving to use fake Windows Update and BSOD...
 Security
SecurityVS Code Extensions Supply Chain Risk: Developer IDE Attacks
Security researchers have uncovered widespread risks in Visual Studio Code extensions, where leaked ...
 Security
SecurityStreaming Platform Halts Live Streams After Content Injection Attack
A prominent live-streaming platform abruptly stopped all live broadcasts following a cyberattack tha...
 Security
SecurityGlassWorm Malware Targets macOS via Trojanized Crypto Wallets
A new macOS-focused malware campaign dubbed GlassWorm is spreading through trojanized cryptocurrency...
 Security
SecurityRondoDox Botnet Exploits React2Shell to Breach Next.js
Security researchers have identified an active campaign where the RondoDox botnet exploits the React...
 Security
SecurityErrTraffic fuels ClickFix scams with fake browser errors
A new service dubbed ErrTraffic is being promoted as a turnkey way to run “ClickFix” social-engineer...
 Security
SecurityZoom Stealer extensions steal meeting data from 2.2M
Security researchers have uncovered a browser-extension campaign dubbed “Zoom Stealer” that collecte...
 Security
SecurityTrust Wallet Users Hit by $7M Crypto Theft Across 2,596 Wallets
Trust Wallet has confirmed a large-scale crypto theft campaign that drained 2,596 wallets, stealing ...
 Security
SecurityHacker Arrested After KMSAuto Malware Hits 28 Million Downloads
A Russian man has been arrested for running a widespread malware campaign disguised as Windows activ...
 Security
SecurityTyposquatted Windows Activation Domain Used to Spread PowerShell Malware
A typosquatted domain mimicking Microsoft’s official Windows activation script site has been used to...
 Security
SecuritymacOS Malware MacSync Stealer Bypasses Gatekeeper, Evades Apple Protection
A newly identified macOS malware variant known as MacSync Stealer is abusing Apple’s code-signing an...