Explanation
Technical explanations and educational content for IT professionals.
Articles with this Tag
 Explainer
Explainer5 Security Mistakes That Expose SMBs to Cyberattacks
SMBs are prime targets for cybercriminals, yet most breaches exploit basic security flaws. Discover ...
 Explainer
ExplainerDMZ Network Explained: Architecture, Security Benefits & Implementation Guide
A Demilitarized Zone (DMZ) creates a critical security buffer between public-facing services and you...
 Explainer
ExplainerRemote Desktop Protocol (RDP) Explained: Architecture, Security Risks & Best Practices
Remote Desktop Protocol enables graphical access to Windows systems over a network, but its widespre...
 Explainer
ExplainerWindows Security Identifiers (SIDs) Explained: How They Work
Security Identifiers (SIDs) are the fundamental identifiers used by Microsoft Windows to uniquely re...
 Explainer
ExplainerIP Addresses Explained: How Networking Identifiers Work
An IP address uniquely identifies devices on a network, enabling communication across local systems ...
 Explainer
ExplainerCPU Architectures Explained: x86, x64, ARM64 and Modern Computing
CPU architectures determine how processors interpret instructions and handle memory, impacting perfo...
 Explainer
ExplainerHigh Availability vs Failover: What’s the Difference?
High Availability and failover are closely related concepts, but they are not the same. Both aim to ...
 Explainer
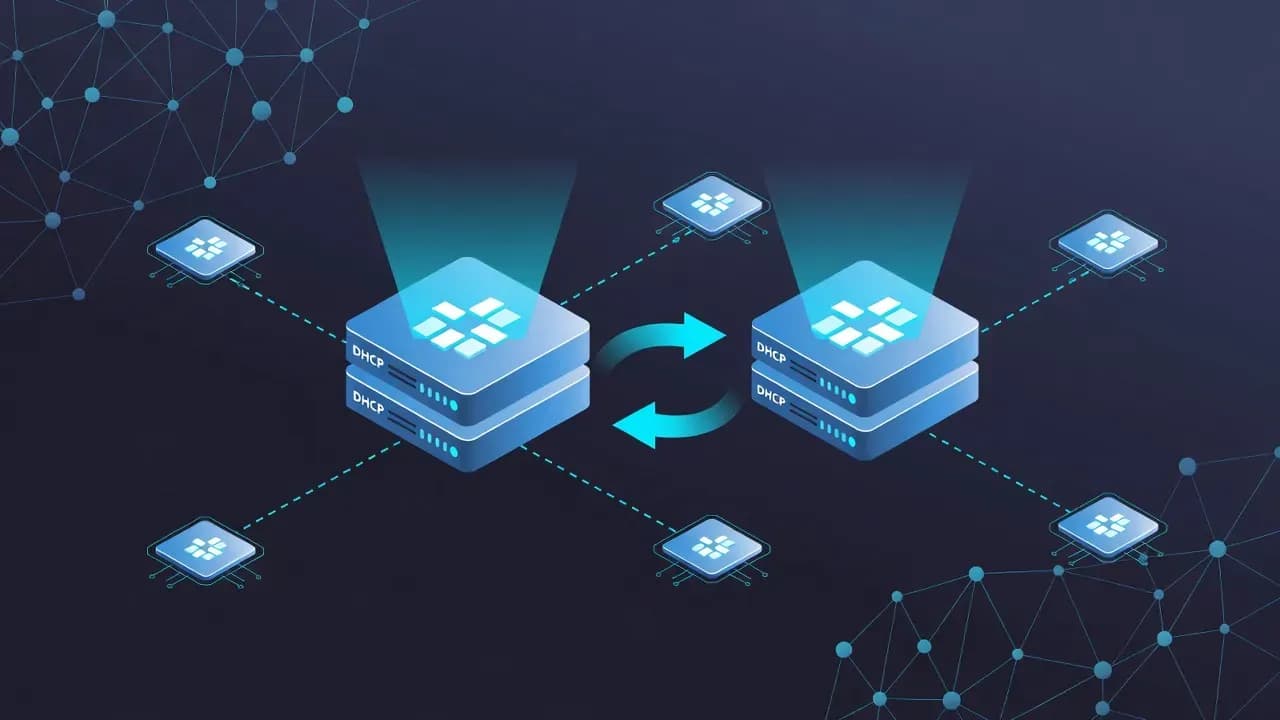
ExplainerWhat Is DHCP Failover and How It Works
DHCP failover is a mechanism that ensures continuous IP address assignment when a DHCP server become...
 Explainer
ExplainerWhat Is DNS Forwarding and How It Works
DNS forwarding is a core concept in network and server administration, yet it is often misunderstood...
 Explainer
ExplainerWhat Is Windows Server and What Is It Used For
Windows Server is Microsoft’s operating system designed for running enterprise infrastructure servic...
 Explainer
ExplainerWhat Is Microsoft Entra ID and How It Works
Microsoft Entra ID is the cloud identity service used to manage users, authentication, and access to...
 Explainer
ExplainerWhat Is Hybrid Join in Active Directory and Entra ID
Hybrid Join is a deployment model that allows Windows devices to be joined to on-premises Active Dir...
 Explainer
ExplainerWhat Is Group Policy (GPO) in Windows Domains
Group Policy is a core management feature in Windows domain environments that allows administrators ...
 Explainer
ExplainerWhat Is Zero Trust Security and Why It Matters
Zero Trust security has become a reference model for protecting modern IT environments. Built on the...
 Explainer
ExplainerWhat Is Conditional Access in Microsoft Entra ID
Conditional Access is a core security control in Microsoft Entra ID that determines how and when use...
 Explainer
ExplainerWhat Is OAuth 2.0 and How It Works
OAuth 2.0 is widely used to secure access between applications, APIs, and users without exposing cre...
 Explainer
ExplainerWhat Is a VPN and How It Protects Online Traffic
Virtual private networks are widely used to secure internet connections and protect data in transit....
 Explainer
ExplainerWhat Is a Firewall and How It Protects Networks
Firewalls remain a foundational security control for modern IT environments. From enterprise network...
 Explainer
ExplainerWhat Is a Data Breach and Why It Matters
Data breaches have become a recurring risk for organizations of all sizes. When sensitive informatio...
 Explainer
ExplainerWhat Is Cloud Computing and How It Works
Cloud computing has transformed how organizations deploy, manage, and scale IT resources. Instead of...
 Explainer
ExplainerWhat Is Phishing and How These Attacks Work
Phishing remains one of the most common and effective cyberattack techniques worldwide. By impersona...
![What is Microsoft Intune? Complete Enterprise Guide [2026]](/_next/image?url=https%3A%2F%2Fanavem.com%2Fuploads%2Fwhat_is_microsoft_intune_endpoint_management_explained_5c28b82974.webp&w=1920&q=75) Explainer
ExplainerWhat is Microsoft Intune? Complete Enterprise Guide [2026]
Hybrid work turned endpoint management into an enterprise risk surface. A single organization can no...