Phishing
Phishing attack awareness, detection, and prevention strategies.
Articles with this Tag
 Security
Security1Password Introduces Pop-up Warnings for Suspected Phishing Sites
1Password adds pop-up warnings to protect users from suspected phishing sites, enhancing its digital...
 Security
SecurityPhishing Attack Uses Stolen Credentials to Deploy LogMeIn RMM
A new phishing attack uses stolen credentials to deploy LogMeIn RMM for persistent access to comprom...
 Security
SecurityOkta SSO Vishing Attacks Use Real-Time Phishing Kits to Steal MFA Codes and Exfiltrate Cloud Data
Okta is warning about custom vishing-focused phishing kits sold "as-a-service" that let attackers or...
Basics of Cybersecurity (2026): A Premium Beginner Explainer (That Actually Teaches You)
A complete beginner explainer: how cyberattacks really happen, CIA triad, the 6-step attack chain, Z...
 Security
SecurityCIRO data breach confirmed to impact 750,000 Canadian investors after August 2025 phishing attack
CIRO says a sophisticated phishing attack first disclosed in August 2025 led to unauthorized copying...
 Security
SecurityReprompt attack showed how a single click could silently siphon data from Microsoft Copilot Personal sessions
Security researchers disclosed "Reprompt," a single click prompt injection chain that could quietly ...
 Security
SecurityReprompt attack exposed a one-click path to hijack Microsoft Copilot sessions
The Reprompt attack combined URL-prefilled prompts with session persistence to hijack Microsoft Copi...
 Security
SecurityBetterment Confirms Data Breach After Attackers Used Its Messaging Systems to Push a $10,000 "Triple Your Crypto" Scam
Betterment confirms a data breach after attackers leveraged its customer communications channel to d...
 Security
SecurityFacebook Credential Theft Surges With "Browser-in-Browser" Popups That Hide Phishing URLs in Plain Sight
Facebook credential theft is being amplified by Browser-in-Browser (BitB) phishing, which renders fa...
 Security
SecurityLinkedIn Comment Reply Phishing: Fake "Policy Violation" Replies Abuse Trust, Notifications, and lnkd.in Links
Attackers are flooding LinkedIn posts with fake comment replies that mimic official policy violation...
 Security
SecurityTelegram Proxy Links IP Address Leak: One Click Can Bypass Your Privacy Proxy and Expose Your Real IP
The Telegram proxy links IP address leak is a privacy failure that looks deceptively ordinary: a use...
 Security
SecurityDiscord "Breach" Claim Looks Like Mass Scraping: HawkSec Auctions 78,541,207-File Dataset From Public Servers
A new "Discord breach" claim circulates as HawkSec promotes an auction of 78,541,207 files. Early in...
 Security
SecurityAPT28 Credential Harvesting Campaign Targets Energy Researchers and Policy Networks with Stealth "Redirect-to-Real" Phishing
An APT28 credential harvesting campaign has resurfaced with a familiar objective and a refined deliv...
 Security
SecurityInstagram denies breach as 17M account "leak" claims collide with reset-email abuse
Instagram is pushing back on claims that its systems were breached after users worldwide reported a ...
 Security
SecurityInstagram Data Leak Reportedly Exposes 17.5 Million Accounts as Attackers Pivot to Password Reset Abuse
A reported Instagram data leak is being treated by threat analysts as a "high leverage" exposure: no...
 Security
SecurityFake Fortinet Sites Weaponize AI Search Summaries to Steal VPN Logins
Fake Fortinet sites are not a new concept, but this campaign is a meaningful escalation because it t...
 Security
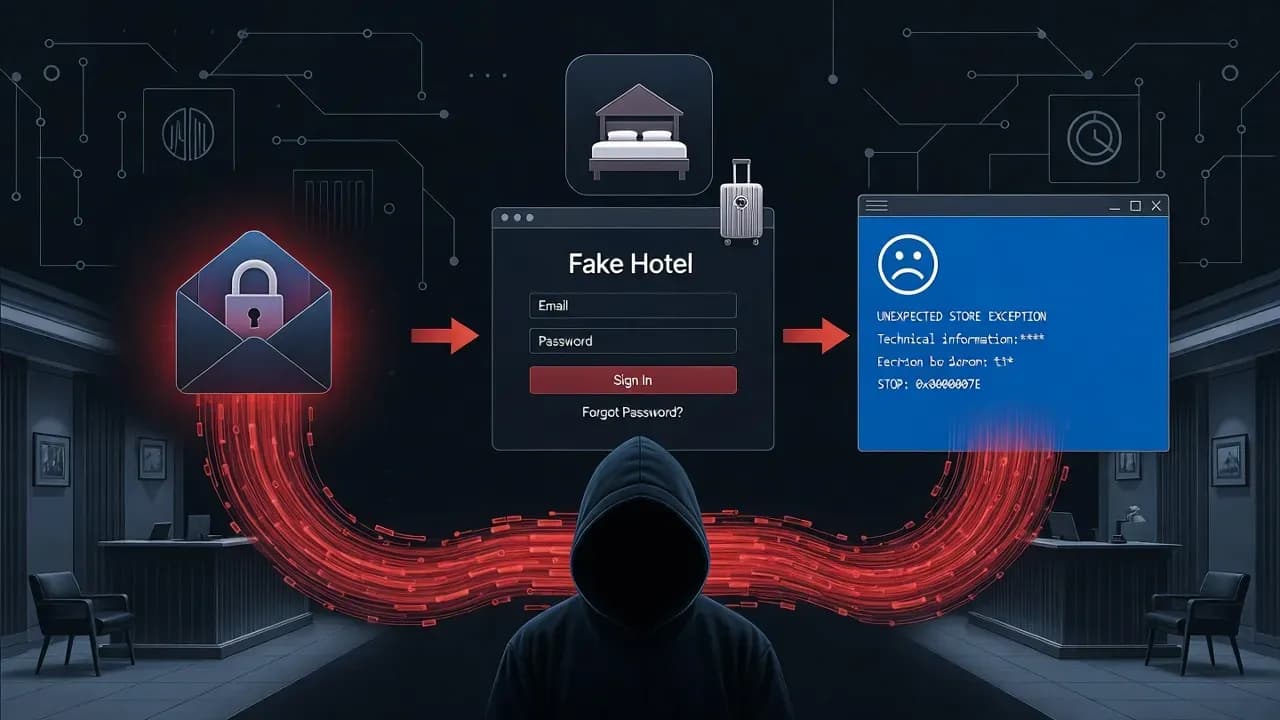
SecurityPHALT#BLYX: Fake Booking.com Emails and ClickFix BSoD Trap Deploy DCRat Malware on Hotel Systems
Threat actors are weaponizing fake Booking.com reservation cancellations and simulated Blue Screen o...
 Explainer
ExplainerWhat Is Ransomware and How to Protect Against It
Ransomware has evolved from a billion-dollar criminal enterprise that can cripple organizations in m...
 Security
SecurityErrTraffic fuels ClickFix scams with fake browser errors
A new service dubbed ErrTraffic is being promoted as a turnkey way to run “ClickFix” social-engineer...
 Explainer
ExplainerWhat Is Phishing and How These Attacks Work
Phishing remains one of the most common and effective cyberattack techniques worldwide. By impersona...